What are VPN protocols?
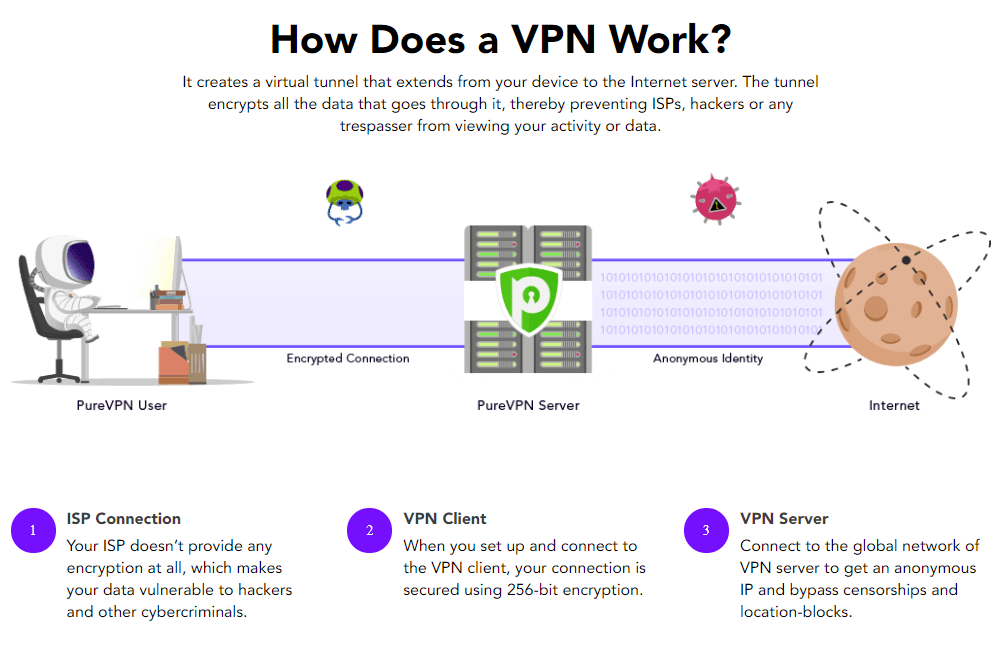
What are VPN protocols? Which VPN Protocol should I use? VPN (Virtual Private Network) is a tool designed to provide you a safe and secure web browsing experience by hiding your identity, encrypting the data and making your activities undetectable. It can help you with free streaming, browsing by connecting you to the world whenever and wherever you are. We have provided you our Best VPN 2023 to help you decide which VPN provider is the best fit for you.
What are VPN protocols? Which VPN Protocol should I use?
When we talk about VPN Protocols, they are basically encryption protocols that determine the extent to which they encrypt the data and how the data will travel between VPN servers and computers.
There is a wide variety of protocols available, each having different characteristics. Some are focused on increasing the speed of browsing while others work on keeping the data more private.
VPN protocols are important. They provide online safety and speed to your online communications and activity. Whether it is the connection speed or online security depends on the VPN Protocol that you are currently using. These operate as tunnels through which your online traffic can pass through. Some tunnels are more secure than others. Some VPN Protocols offer amazing streaming speeds.
There are many types of protocols available, each having different strengths and capabilities. Some protocols are mobile devices friendly. Others can be installed on your Wi-Fi router as well. Some offer better internet protocol security. Choosing a VPN protocol with PureVPN is important if you want to enjoy the best browsing experience.
There are a number of VPN protocols which are used to secure the transferring of data traffic over a public network. Each protocol differs in the way data is kept secure. NordVPN uses OpenVPN and IKEv2/IPSec as standard protocols for its desktop and mobile applications and TLS v1.2 for its encrypted browser extensions.
List of VPN protocols:
- Open VPN
- L2TP (Layer 2 Tunnel Protocol)
- IPsec (Internet Protocol Security)
- PPTP (Point-to-Point Tunneling Protocol)
- SSTP (Secure Socket Tunneling Protocol)
- IKEv2 (Internet Key Exchange Version 2)
- SSL (Secure Socket Layer)
- TLS (Transport Security Layer)
- Wireguard
- Soft Ether
5 Best VPN protocols:
Here we will discuss top 5 protocols along with their Features, Pros and Cons.
PPTP (Point-to-Point Tunneling Protocol)
PPTP is the oldest protocol launched in 1995, although a number of new protocols have replaced it, it is still in use because of the speed it provides. With great speed, the encryption standard is highly compromised. PPTP is obsolete technology and no longer used for sensitive data, So if the privacy of data is your priority, it is not for you. When bandwidth-intensive usage is required like live streaming and geo-unlocking, you can definitely rely on it.
Features:
- Compatibility: Windows, macOS, Android, iOS, Linux, and more.
- Speed: Fast
- Security: Least secure of all protocols
- Encryption: 128-bit
| PROS | CoNs |
| Great platform compatibility | Poor privacy |
| Super-fast | Blocked by the firewall |
| Easy to use | |
| Great video streaming |
Open VPN:
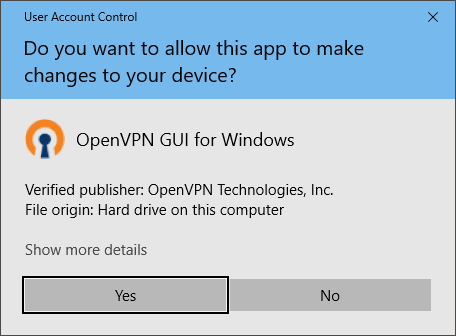
It is one of the newest and finest protocols introduced in 2001. As the name suggests it is open-source, safe and adjustable of all the VPN protocols. Open VPN is constantly changing according to the needs of cybersecurity, So you can consider it is the best protocol in terms of privacy. The best part is it offers cross-platform compatibility which means you can use it on almost every device. It is not built into desktop, laptops or smartphones, So it is used by Third Party VPN clients and paid VPN providers use it as a default protocol. Like any other HTTPS website, it uses a custom protocol for security and relies on OpenSSL. It is difficult to block because it manages to behave like normal internet traffic, having the ability to be configured to use any port. It is not that fast like PPTP but it can definitely protect your privacy.
Open VPN has two entirely different variants:
OpenVPN-TCP (Transmission Control Protocol): It deals with the transmission and exchange of data along with a confirmation packet that assures you that your data has been delivered. You can say it helps with the reliable transmission, interception, and delivery of your data.
OpenVPN-UDP (User datagram protocol): It works to reduce the latency rate by decreasing the number of checks to ensure data delivery on time. So, it can work best for gaming and streaming.
Feature:
- Compatibility: Windows, macOS, Android, iOS, Linux, Routers, etc
- Speed: Fast (with complete security)
- Security: Best with Security
- Encryption: Extendable up to 256-bit
| Pros | Cons |
| Highly flexible | Difficult setup procedure |
| Customized as per need | Requires third-party software |
| Many encryption algorithms | |
| Cross-platform compatibility | |
| Extremely secure |
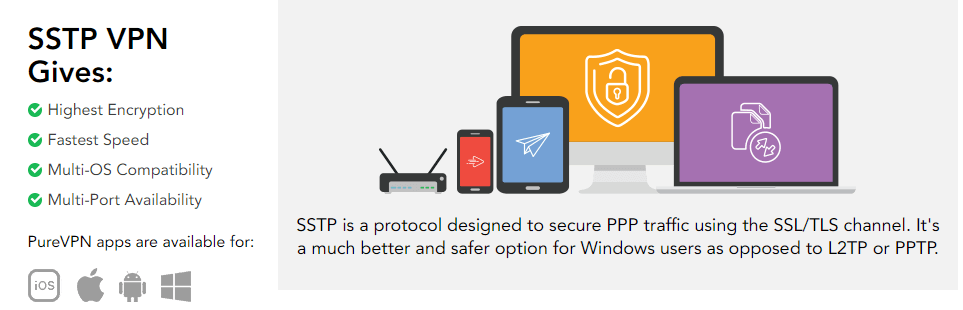
SSTP (Secure Socket Tunneling Protocol)
SSTP is a protocol launched by Microsoft with windows vista but due to security errors company itself declared in 2014 some known issues about this protocol. SSTP uses an outdated encryption standard (SSL 3.0) having some security issues Even with such insecurities it is considered as the most robust item by Microsoft because it works better than many other outdated VPN protocols.
It has good platform compatibility but it definitely works best with windows. Macs and Linux will face a hard time to install SSTP. So you can assume that only die-hard fans of windows use this protocol. It is better than L2TP as it can cross firewalls well but it can never beat Open VPN. In terms of speed, it is much like an Open VPN Protocol.
Features:
- Compatibility: Windows (Best), macOS, Android, Linux (Fair)
- Speed: Average
- Security: Best with Security
- Encryption: Extendable up to 256-bit
| Pros | Cons |
| Secure to some extent | Best only with Microsoft |
| Support many encryption algorithms | Average platform compatibility |
| Easy to use | |
| Bypass many system firewalls |
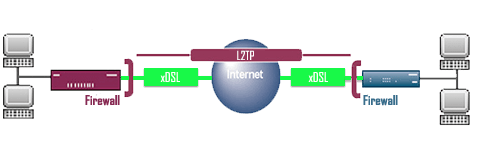
L2TP (Layer 2 Tunnel Protocol):
This protocol is rarely used alone as it is not meant for encryption. This comes with IPsec (a great encryption protocol). Together they make a bundle with complete privacy and security.
L2TP/IPsec is compatible with smartphones and desktop computers. It would be great for average Internet users who demand good security and hassle-free use of the Internet. It offers you average speed as it encloses the data twice which causes the speed to slow down. Some experts find this protocol vulnerable or compromised as IPsec was developed by US NSA (National Security Agency). So, NSA can track all your online activities.
Features:
- Compatibility: Windows, macOS, Android, Linux
- Speed: Fair
- Security: Best with Security
- Encryption: Extendable up to 256-bit
| Pros | Cons |
| Easy setup | Compromised by NSA |
| High standard security | Fair speed |
| Good platform compatibility | Blocked by firewalls |
IKEv2 (Internet Key Exchange version 2):
IKEv2 is the newest protocol introduced by two giants Microsoft and cisco. It’s basically as tunneling protocol much like L2TP it is used as a bundle with IPsec. You can call it a stable protocol because it has the ability to keep you connected even with the fluctuations of your internet connection. Being a Microsoft production it works well with windows, it is easier to set up than Open VPN.
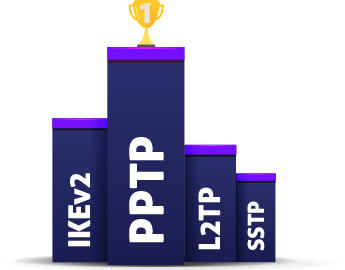
It is much appreciated by users because it is user-friendly, secure and wireless. As it is good at managing connection failure it is best for mobile phones having 3G and 4G LTE. When we talk about speed you can consider this on top of the list.
Features:
- Compatibility: Windows, macOS, Android, Linux
- Speed: Fast
- Security: Best with Security
- Encryption: Extendable up to 256-bit
| Pros | Cons |
| user-friendly | Blocked by firewalls |
| Fastest of all | |
| Stable | |
| Very secure |
Summary:
| Open VPN | Flexible protocol with Safest encryption and average speed |
| L2TP/IPsec | Tunneling protocol offering good speed |
| PPTP | Offers great speed, so good for games and video streaming |
| SSTP | Offers the best security |
| IKEv2 | Secure, user-friendly, fast and Open |
Conclusion:
What are VPN protocols? Which VPN Protocol should I use? We hope we answered these questions for you. Each protocol is different in its characteristics, some are good with speed while others with encryption. We can draw an inverse relationship between speed and level of encryption. When you increase speed, the level of encryption is compromised and vice versa. But there are some protocols like Open VPN and IKEv2 that try to keep a good balance. The Selection of a protocol completely depends on the need and priorities of a user. If you do not deal with any confidential and sensitive data and only concerned only speed for gaming and streaming, you can use PPTP. But if you need some security, privacy and good speed, you can choose IKEv2. Our choices for Best VPN Providers 2023 will help you find the Best VPN Provider for your needs with the best VPN Protocol available.